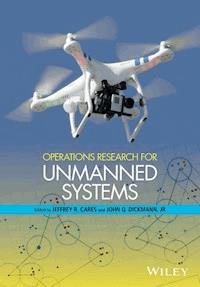
Operations Research for Unmanned Systems ebook
0,0
439,99 zł
439,99 zł
-50%
Zbieraj punkty w Klubie Mola Książkowego i kupuj ebooki, audiobooki oraz książki papierowe do 50% taniej.
Dowiedz się więcej.
Dowiedz się więcej.
- Wydawca: John Wiley & Sons
- Kategoria: Literatura popularnonaukowa
- Język: angielski
The first edited volume addressing analysis for unmanned vehicles, with focus on operations research rather than engineering * The editors have a unique combination of extensive operational experience and technical expertise * Chapters address a wide-ranging set of examples, domains and applications * Accessible to a general readership and also informative for experts
Ebooka przeczytasz w aplikacjach Legimi na:
Liczba stron: 627
Rok wydania: 2016
0,0
Oceny przyznawane są przez użytkowników Legimi, systemów bibliotecznych i innych serwisów partnerskich. Przyznawanie ocen premiowane jest punktami Klubu Mola Książkowego.
Legimi nie weryfikuje, czy opinie pochodzą od konsumentów, którzy nabyli lub czytali/słuchali daną pozycję, ale usuwa fałszywe opinie, jeśli je wykryje.